Prerequisites
Windows Security Events via AMA Connector vs. Security Events via Legacy Agent Connector
The Windows Security Events via AMA Connector has the following differences from the Security Events via Legacy Agent Connector:
Benefits:
- Manage collection settings at scale
- Azure Monitoring Agent shared with other solutions
- Performance improvements
- Security improvements
Limitations:
The Azure Monitor Agent is released in preview and is supported with the CSPM plan and Microsoft Defender for Servers Plan 2.
Requirements:
non-Azure VM’s/devices require Azure Arc.

Installing AMA requires Azure arc
- Windows security events Via AMA
- This will create data collection rule
- You can choose from events.
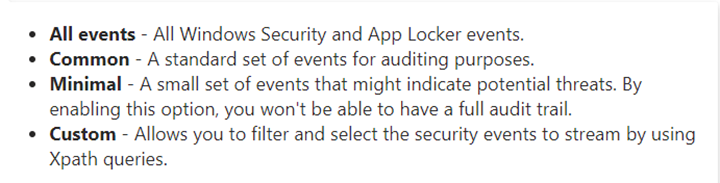

Data collection rules structure
Data collection rules in Azure Monitor – Azure Monitor | Microsoft Learn

We will use the Custom and use the Xpath to choose the specific events.
Custom allows you to specify other logs or to filter events using XPath queries. For XPath queries you can enter up to 20 expressions in a single box, and up to 100 boxes in a rule. The Azure Monitor agent supports XPath queries for XPath version 1.0 only.

This is example
$XPath = ‘*[System[EventID=1035]]’
Get-WinEvent -LogName ‘Application’ -FilterXPath $XPath
To choose the event
Go to event Viewer
Filter current log
Choose the events you need.
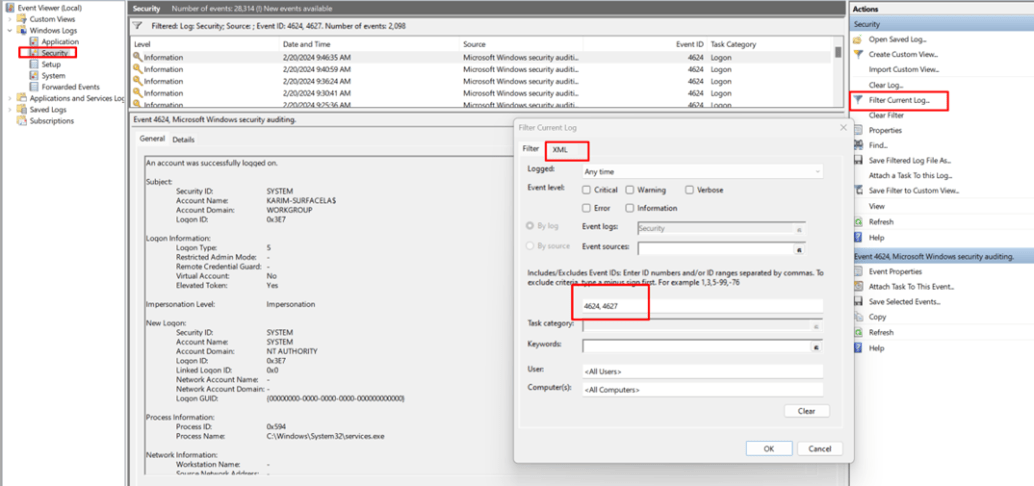
Then Go to XML and choose edit query manual
Copy starting from the *[system til ]
“*[System[(EventID=4624 or EventID=4627)]]”

Test with PowerShell
Test it with PowerShell
$XPath = ‘*[System[(EventID=4624 or EventID=4627)]]’
Get-WinEvent -LogName ‘Security’ -FilterXPath $XPath

you must append the log type category followed by an exclamation point (!).
System!*[System[(EventID=4624 or EventID=4627)]]
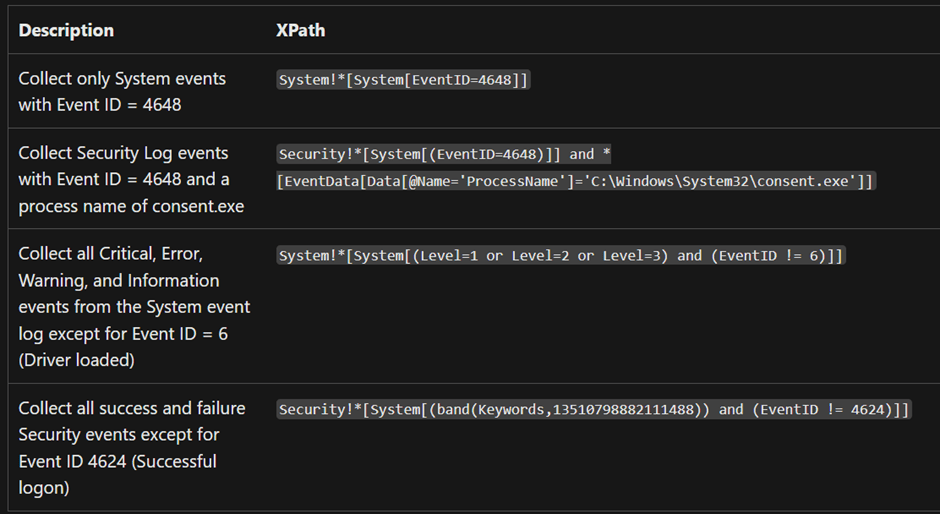

More details will be found here
