In this article we will be talking how to protect and secure your information using Microsoft protection suite.
We will be more concerning on a new feature in the DLP for endpoint devices
We will talk on how the information is created, edited and transferred outside the organization
Table of contents
What is information life cycle steps?
How to create protection policy for files
How to monitor files and policies
What are the products used?
How to monitor
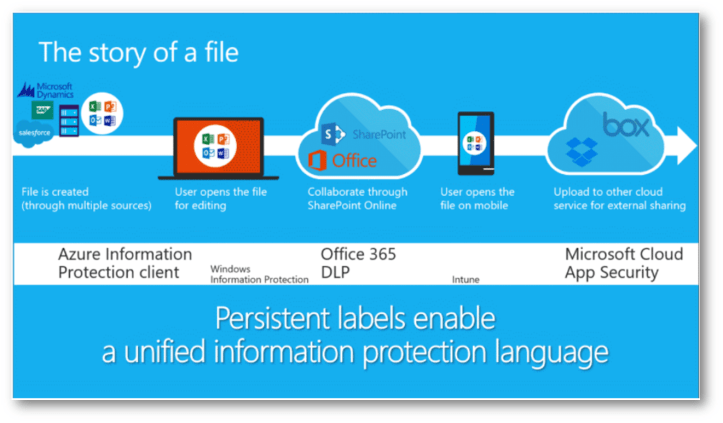
- File is created
Regardless of where the file is created, sensitivity labeling in Office apps can enforce information protection based on the labels attached to the data.
- User edits the file
The label is updated based on the user’s changes and the content’s sensitivity. This ensure the file has the right protection.
- User shares the file with another user in the organization
As an additional layer of protection, Data Loss Prevention (DLP) policies in Office 365 help prevent the accidental or inadvertent sharing of sensitive documents and emails.
-
User opens the file on their phone
If a user receives and opens the data on a mobile device, Intune enforces protection of the data.
-
User uploads the file to another cloud service such as Dropbox
If a user uploads the data to other clouds for external sharing, services such as Microsoft Cloud App Security can apply policies based on the data’s labels.

Microsoft 365 security center and azure
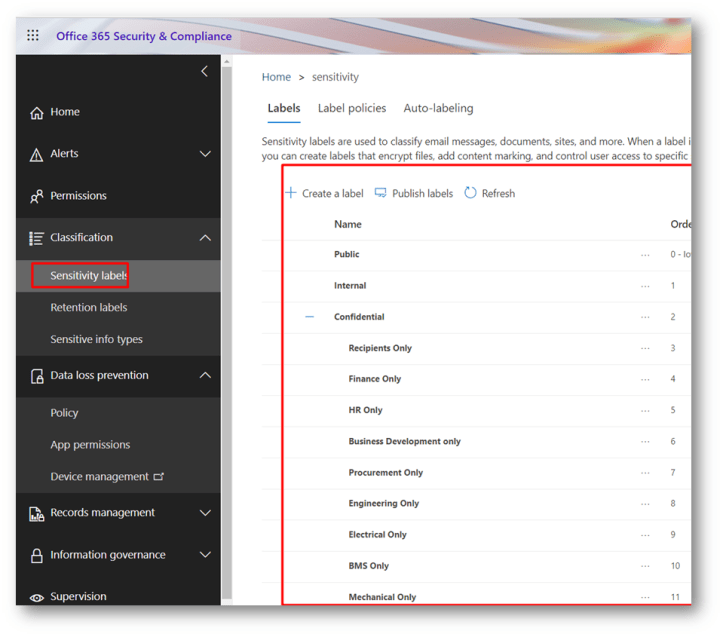
Create labels
AIP classic (old version)

UL new version
How to create DLP for Endpoint devices
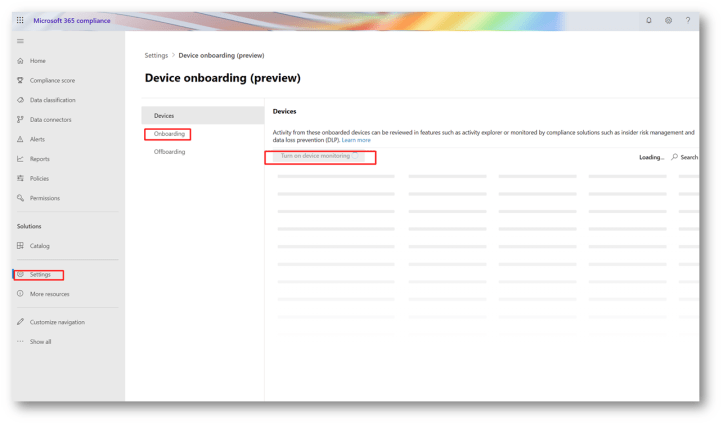
First you need to onboard the devices either by
Microsoft defender ATP or by going to compliance center
As described in the onboarding devices
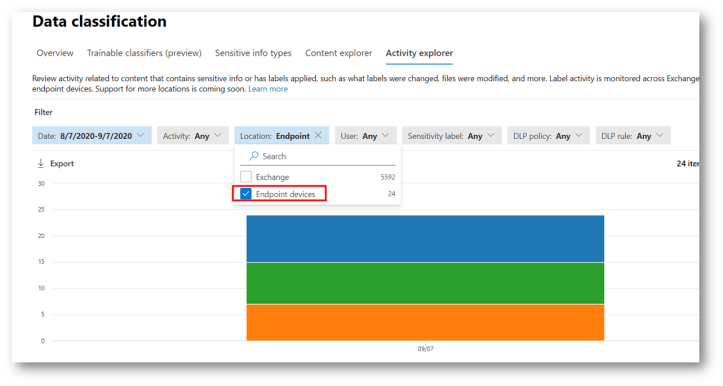
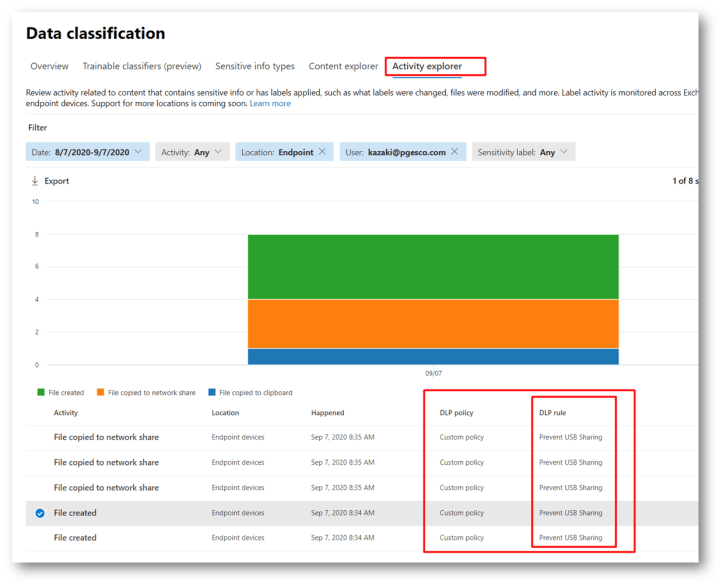
Also you will be able to View Endpoint DLP data in activity explorer
Now endpoint appears in the activity explorer
You can start first by excluding some noisy paths

Start creating the policy
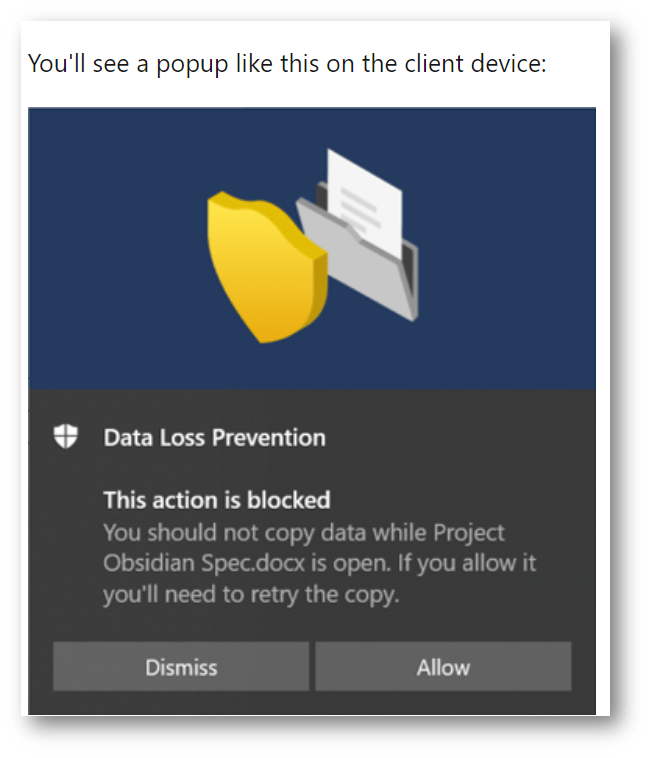
In this demo I ll block the devices from USB
The Endpoint is only available in the compliance center
https://compliance.microsoft.com/datalossprevention?viewid=policies

In the location choose the devices
Note: it is in preview so please use it as a test and choose a user or group don’t apply on all

Start creating your Rule

Ill create for usb to Audit only

My test is a set the label to internal
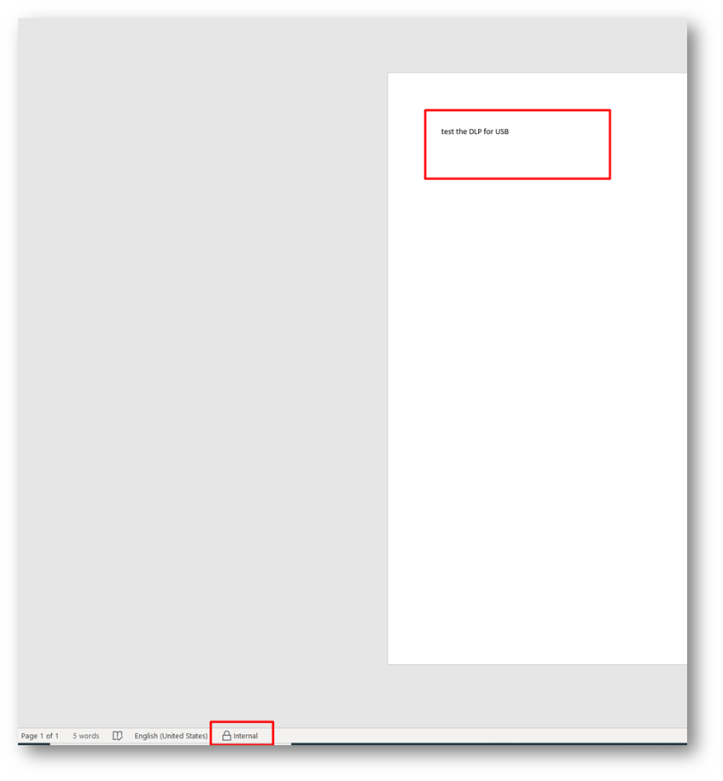
You must check the activity explorer
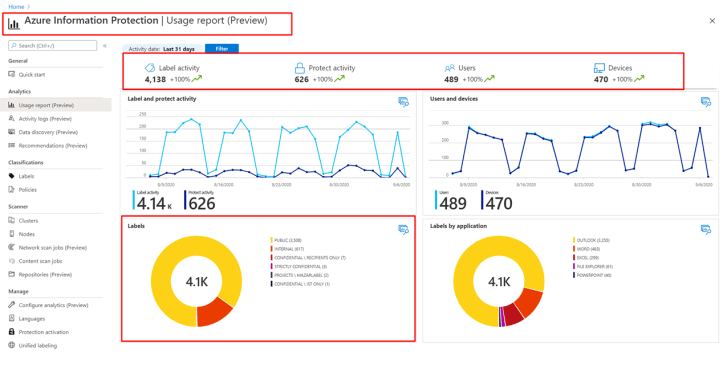
Monitor and analyze sensitive data
File created or user edit file
https://security.microsoft.com/labelanalytics

For DLP

